This post provides details on analysing and investigating AnyDesk log files recorded in the machine running in Windows operating system.
Introduction
AnyDesk is a remote desktop application to manage computers remotely. This offers VPN, remote management, file transfer capabilities. System administrators use this application to provide remote support to their users. Threat Actors(TA) can abuse this application to remotely manage the compromised computers and to exfiltrate data.
Following log files related to AnyDesk applications are recorded in the directory C:\ProgramData\AnyDesk.
1.Connection_trace log
2.Ad_svc trace log
Along with the above log files, these are the additional artefacts that are recorded in the Windows machine. The below mentioned log files are recorded in the directory C:\Users\<User profile>\AppData\Roaming\AnyDesk.
1.Ad trace log
2.Chat directory that includes chat log
As an investigator, you can analyse these log files to understand the TA activity.
Threat Actor exfiltrate data through AnyDesk application
TA after compromising a machine, TA can install AnyDesk application in the victim machine to transfer data to TA infrastructure.
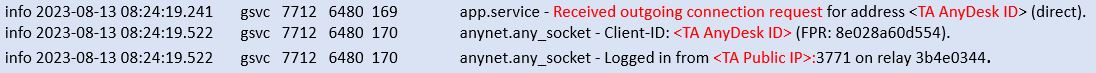
Analyse ad_svc trace log in victim machine to identify outgoing connection details, that includes TA AnyDesk ID and their public IP address.
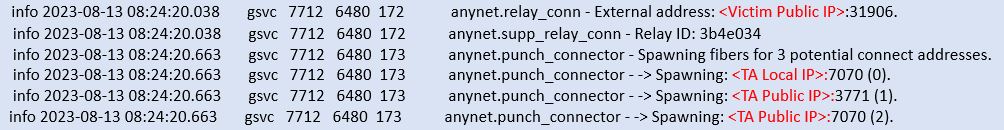
In the same log file, we can identify victim public IP, TA local and public IP address.
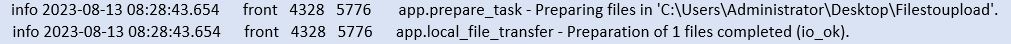
AD trace log file in victim machine will record data transfer activity. We can see the directory of the transferred files and status of the transfer activity. The name of the files transferred, and the file size will not be recorded in the log file. We may need to analyse the Windows master file table to identify the files recorded in the identified directory.
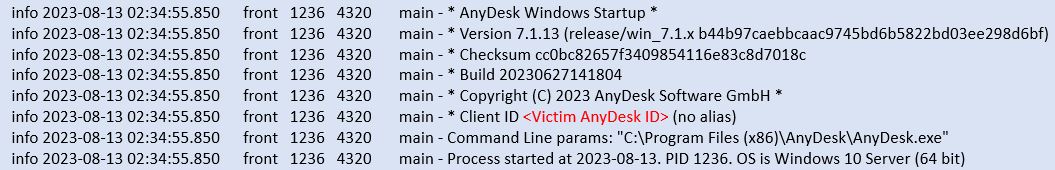
AD trace log file in victim machine will record details about AnyDesk application used in the victim machine.
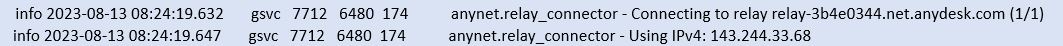
In ad_svc trace log, we can see the outgoing connectivity to AnyDesk relay server. Once we identify the relay server IP address, we can analyse the network firewall connection logs from victim machine to AnyDesk identified relay server. The network connection logs record the connection size details, through which we can estimate the transferred file size.
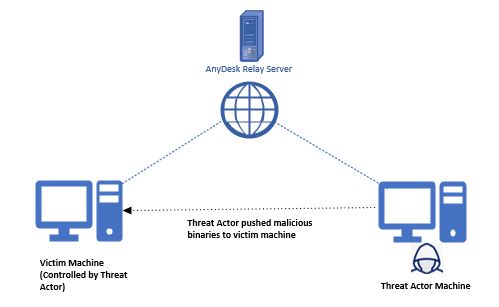
Threat Actor pushes malicious files through AnyDesk application
TA after compromising a machine, TA can install AnyDesk application in the victim machine to push additional malicious binaries from TA infrastructure.
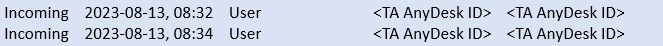
connection_trace log in victim machine will record the incoming AnyDesk connection details. This log will record the TA AnyDesk ID.
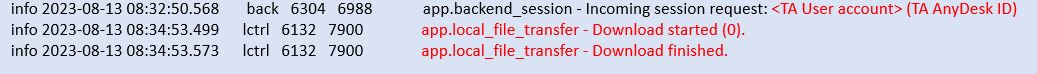
ad_svc trace log in victim machine will record the incoming connecton details, that includes TA public IP, TA local IP, TA AnyDesk ID, AnyDesk relay server details.
ad trace log will record file downloaded activity, but no detail about the files downloaded will be recorded.